System
integrator role in SSA Business
Yam,
you know SSA is stands for Security Safety Automation (SSA Integrate). A security systems
integrator by definition specializes in bringing together subsystems into a
whole and ensuring that those subsystems function together. When the goal is
physical security, those subsystems might be Video surveillance, Access
control, Intrusion, FDA or Emergency notification, BAS, computer networks and
more. Some security suppliers have established business simply on the
procurement and installation of systems predefined by others. More fully
developed are considered ‘design-build’ integrators. However the most capable
security integrator is a full service provider capable of supporting your
operations in every phase of the security system lifecycle:
1. Security risk or needs assessments,
2. System engineering and design for
the major technologies,
3. Broad access to the leading product
lines,
4. Custom engineering when required,
5. Alternate investment options,
6. Procurement, staging, installation,
commissioning and training,
7. Full lifecycle service and
maintenance,
8. System functional and technology
upgrades.
A
client who selects an integrator fully capable in all the above can then take
advantage of his unique perspective on what are the key ingredients for
successful development of a physical security program that is supportive of a
healthy enterprise.
Working
with a full service security provider also reinforces quality. Consider why
this is so. If, for instance, the integrator offers long term service and
maintenance for the system he installs, then both the service provider and the
customer are motivated that the design should be solid and the installation of
high quality. And if the integrator can offer attractive long term financing,
even operational leases, then he again has a further stake in the caliber of
the security provided.
System integration is defined in engineering as the process of bringing together the component sub-systems into one system (an aggregation of subsystems cooperating so that the system is able to deliver the overarching functionality) and ensuring that the subsystems function together as a system, and in information technology as the process of linking together different computing systems and software applications physically or functionally, to act as a coordinated whole.
System integration is defined in engineering as the process of bringing together the component sub-systems into one system (an aggregation of subsystems cooperating so that the system is able to deliver the overarching functionality) and ensuring that the subsystems function together as a system, and in information technology as the process of linking together different computing systems and software applications physically or functionally, to act as a coordinated whole.
System
Integrators in the automation industry typically provide the product and
application experience in implementing complex automation solutions. Often,
System Integrators are aligned with automation vendors, joining their various
System Integrator programs for access to development products, resources and
technical support. System integrators are tightly linked to their accounts and
often are viewed as the engineering departments for small manufacturers,
handling their automation system installation, commissioning and long term
maintenance.
Are there tangible ways that we see
interoperability trending in the industry?
There is certainly movement toward
standard-compliant products but it is slow. I attribute this mainly due to
engineers reusing portions of old or outdated specs along with their lack of
knowledge of the current product offerings. IP cameras will help move the
standards along since more and more clients are aware of megapixel technology
and it forces the engineers to become more current.
Where do you see underserved or untapped
opportunities for security systems integrators to provide integration and
automation expertise?
Video
and access technology have the potential to be integrated well beyond the
traditional Big Brother stereotype applications. One example is warehouse distribution
and processing applications where repetitive tasks performed incorrectly can
slow production or cause injuries. Video analytics could be modified to monitor
physical movement and monitor improper technique that could lead to injuries.
These
videos could initiate notifications to HR and management staff to alert them to
potential problems before they occur. Access to machines and forklifts could be
controlled through HR records. Integrating the access system to training and
safety certifications could help reduce unqualified employees from accessing
and enabling critical operational systems. Security could monitor the
traditional video footage, HR could assemble incident reports tagged with the
video and management could build and expand training programs with real world
examples.
Another area of potential growth is
the smart building. A fully integrated structure including security, lighting, HVAC
and building controls that provides a return on investment along with the
ability to remotely manage a site.
How can a locally-based or small regional
company have successes in enterprise-level organizations?
Local
companies can have a distinct advantage over the national integrators. First,
the small or regional company must be technically advanced and focused on
cutting-edge technology so they can provide a value to an enterprise-level
client. They must also network with similar dealers with related product lines
so they can establish an installation network throughout North America or the
regions they are required to service. They can also become an agent for the
enterprise client and coordinate all installations and manage that system for
that client. Compare that level of service to the big integrators. Yes, they
have a handful of talented individuals that truly get the big picture and these
men and women travel the country and the world implementing systems. But once
the job is completed, they’re off to the next one and you may never see them
again.
How can smaller integrators differentiate to
better compete?
A commitment to service is the local integrators greatest
strength. Through continuing education of its technical staff and building
working relationships with clients, a local integrator can react quickly and
see the big picture of their customers’ needs and requests. As the IT
department begins to dominate the physical security industry the local
integrator can help be a bridge between the security professionals and the
sometimes frustrating “smartest man in the room” syndrome of the IT staff .
Most integrators have a great respect for the current and former local and
national law enforcement professionals we work with every day. Their knowledge
of where and why a camera is placed and how to implement the concentric rings
of security, lighting control and placement is invaluable. The human element of
security beyond pure technology is something that some IT professionals do not
always grasp. Integrators can successful bridging that gap when they strive to
clearly communicate with both departments.
What is the Solution Development Process With
a Full Service Systems Integrator?
Risk Assessment. Your integrator should be
able to assist or guide you in this first step toward development of a security
solution. The industry standard for this is the ASIS 7-step general security
risk assessment guideline. The guideline defines a process which starts with
identification of assets and risk events and ends with a solution cost benefit
analysis. Properly done the end product is not only the security you want and
need but a documented rationale for the investment.
Financial
Options. Similar to many
internal enterprise processes the best electronic security solution is
sometimes planned to be phased-in over time to give the client the best
possible security function progressively. Nonetheless a full service integrator
enables you to tailor acquisition of enhanced security in a manner which meets
your needs. As an example, reasonably priced capital leases can push the cash
flow impact of security into outer years. Due to current accelerated tax
depreciation in effect these leases can in some instances reduce the net cost
below that of an outright purchase. If a full service integrator has the
internal resources – service fleet, repair department, stocked inventory, etc.
– to maintain their installed systems they may also offer and administer
operational lease programs to the security solutions they provide. These leases
differ from capital leases in that ownership of the physical security equipment
is retained by the service provider yet the site installation and its sustained
operability is available as a monthly service fee.
Design. The functional design should clearly
define for the end user the extent of the solution’s protection. It may involve
multiple technologies for the most effective solution. Minimizing the burden
placed on general staff to maintain security and respond to emergencies should
typically be a demonstrable objective.
Value
driven component selection may require a number of different supplier sources.
Exterior components will be weatherproof, interior components will be vandal
and wear resistant as needed. System operation will be well protected from the
dangers of tampering, surges, electrical strikes, etc. as well as single points
of failure if possible. A good design will not dead-end the customer but
position the delivered security solution for adaptation to meet anticipated
future needs. Good designs may even enhance as well as protect enterprise and
site operations.
Installation &
Commissioning. The installation should
conform to and even exceed state and federal regulations and guidelines and be
performed by licensed personnel as required. The installation should be safe
for all onsite, reflect excellent workmanship and conduct should be courteous
and respectful to all involved. System configuration should be performed by
individuals with good system knowledge. The end user training should be
complete enough to address at least typical daily tasks and provide them the
resources they need to reinforce the training and administer further if
required. This is most likely provided by a resource positioned to be a partner
in meeting your security needs.
System Maintenance and
Service. The overarching goal is
to maintain the operability of your security solution with the same
effectiveness experienced as it was commissioned. But electronics degrade and
fail and sites often continuously require system tweaks as they grow. A good
service program will make available to you certified service personnel as well
as standard and emergency response times you can depend on. The best providers
will often maintain stock for repair and loan and even have in house bench
repair capability for rapid, cost effective turn around. And if you have
outgrown your security systems or they are generally showing their age a good
provider can offer mid-life upgrades and/or ‘system refreshes’ which
progressively secure your operations and people.
Enterprise Security is Not A
Commodity.
Why
is enterprise physical electronic security more than just a commodity to be
procured? Because the security risks are multiple, varied and changing. Some
which occur infrequently are the most potentially damaging. An outside
perspective developed from meeting a variety of client needs can help prioritize.
The current solution state of the art is technical, multidisciplinary and
rapidly evolving. There is not a consumer protected design-bid-build process
which guarantees success. Only a subset of security industry service providers
are equipped and positioned to reliably assist you from needs development
through to system maintenance.
Trust on your selective System Integrator or Solution Service Provider.
System Integrator who really work in different system with different brand system, they are know who or which OEM has good service support. No one integrator is wise for all product. System Integrator surve customer. OEM will not provide service.
Trust on your selective System Integrator or Solution Service Provider.
System Integrator who really work in different system with different brand system, they are know who or which OEM has good service support. No one integrator is wise for all product. System Integrator surve customer. OEM will not provide service.
Tips to choose Best System Integrator in India
·
Choose
a systems integrator who has a list of successful projects with appreciation letter
from customer. Check references, talk to their clients and take reviews. Find
out for how long they have been in the field.
·
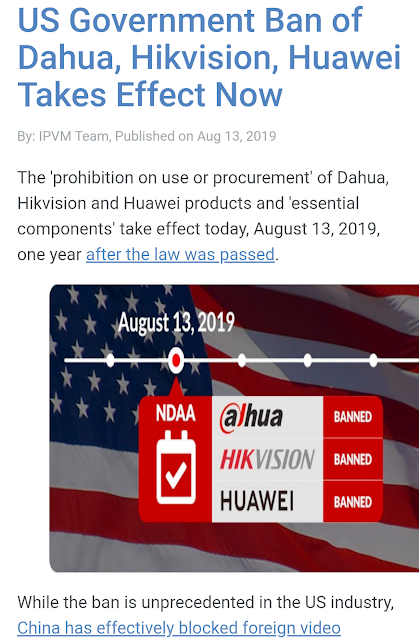
System
Integrator should have long-term relationship and close ties with the leading
OEMs. These relationships allow an integrator to keep up to date on new
technologies, get the best prices, and provide you with the most complete
support network available. The best integrators focus on customer needs and
build solutions using best of breed technologies. They should have a broad
range of products they have worked with and enough staff to handle different
areas of the project.
·
The
integrator should prove that they understood your requirements. Take Quote from
multiple System Integrators. Be especially careful if you get lower price than
expected or that others have quoted. Make sure the system integrator doesn’t
over commit during negotiations.
·
System
Integrator should have specialized expertise and that can be applied
to create an architecture that ensures security, flexibility, and scalability
to meet your IT service availability demands. Focus on their knowledge,
techniques and skills. Make sure they have full knowledge of system engineering,
as well as sufficient experience to handle your project.
·
If
you don’t have in-house expertise for making the integrator selection, consider
hiring a third-party technical consultant to establish selection criteria
and/or participate in the review process. Get involved at the zero level in the
planning, simulation, detailed layout, software handling techniques and
maintenance requirements as much as you possibly can in order to get the
biggest possible benefits. In this point our Writer can help, you may connect
with this article writer.
·
Keep
up-to-date milestone records during the course of the project. If you have to
replace an integrator, refer to the specification and decide on a fair
settlement covering payment for all completed deliverables. System Integrator
should have a knowledge transfer process in place. This ensures you have the
time and resources necessary to ensure your team understands the work product
and can continue on – independently and successfully.
·
Look
for an integrator that listens to your needs, communicates well, and provides
customized solutions for your business.
·
Select
an integrator that has a large, experienced engineering core with a holistic
understanding of your entire ELV ecosystem. This will facilitate better
design, deployment and support.
·
System
Integrator 2/3 team member should have Membership their own technology field like:
ASIS International, SIA (SECURITY INDUSTRY ASSOCIATION), FSAI, National Safety
Council.
For a Free
Consultation Call: +919903280406
Please find below my details.