IoT is future of Video Technology
The
Internet of Things is about connecting network-enabled devices and exchanging
data between them. This offers great potential for improving processes wherever
information needs to be exchanged securely and quickly. It enable devices and
add much more value than they have had so far. For this, there is no better
example than security cameras. With IoT we’re able to push and pull nuggets of
intelligence from sources we never considered before: environmental sensors,
pressure plates, door lock timers and much more. It’s helped us break through
the constraining mindset that security systems are strictly single-purpose.

Acting
alongside other sensors, such as motion or smoke detectors, security cameras
have been in use for a long time, however without being connected to each other
through data networks. Growing demands for smart video surveillance in public
spaces, commercial buildings, public transport and other areas and
the rise of IoT will drive for the further integration of these cameras
systems. Let's see how video surveillance has evolved to this day and where the
journey is heading.
The past: standard security surveillance systems
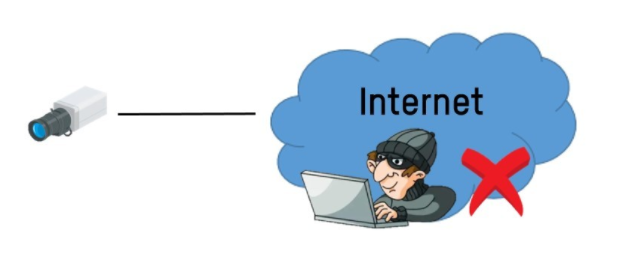
Closed-circuit
television systems (CCTV) have demonstrated that they can do what they're
supposed to: give humans a better eyesight on the security situation in order
to reduce security incidents. CCTV cameras can only show and record video
footage and not much more beyond that. As they do not understand what they are
watching, they are also unable to do anything about it.
To fight
theft, violence, vandalism or fire effectively, cameras must be able to detect
and interpret such incidents by themselves. They must also have the capability
to cooperate with other systems, such as alarm systems.
This is
where the Internet of Things comes into play. It connects network-enabled
cameras with other devices and systems that perform other tasks and turns
security surveillance into smart safety and security management.
Video
surveillance systems built the largest segment in our country. That’s why today
modern camera systems are widely used in many areas of life, retail, commercial
buildings, stadiums, transportation and public spaces in cities.
Security
cameras frame the next technological step in the security surveillance
evolution…
The future: smart security surveillance
The times
when video surveillance systems only deliver video that must be continuously
observed by humans are over. Machines able to record and analyse video data in
one go are already available, and they can provide security managers with deep
insights instead of single pieces of information.
This will
significantly improve security and security-related processes in many areas and
industries by enabling faster and more insightful response to any sort of
incidents.
Future
security surveillance essentially combines 3 technologies that will completely
change the game: computer vision, automation and deep-learning, driven by
powerful processors and apps on cameras in the IoT. Let's take a quick look at
these technologies.
Data is the new digital oil
All these
devices at their most basic, simply collect data. This information is used to
streamline, manipulate and measure the way you interact with the world. From
your online habits to your physical day-to-day routine – every single thing you
do or don’t do is, or will very soon be, monitored.
In the
case of connected ‘things’ – now known as ‘smart devices’ due to their ability
to collect and transmit information – each one sends bytes of data over the
internet to an application that interprets and collates that data into valuable
insights. Your service provider and the product manufacturer can then use those
insights to achieve a variety of objectives – from improving the device’s
performance, and your experience of using it, to identifying how or when they
should be selling you extra services or products.
What precisely is connecting all of these IoT
things
2G, 3G and
4G are terms that we all know and understand well but how about radio, Wi-Fi,
NB-IoT or LPWAN? There are various types of connectivity that can underpin the
Internet of Things and these latter ones are arguably the most widely used
outside of pure cellular connectivity.
When we
talk about the ‘internet of things’ it’s not immediately clear which type of
‘internet’ connectivity we’re referring to because many devices are now being
designed to intelligently select the connectivity that best suits its needs,
based on the following three things:
Power
consumption –
How much power does the device or sensor need to operate?
Range –
Does it need to connect and send data over great distances?
Bandwidth –
Will it transmit small or large amounts of data e.g. low bandwidth and high
bandwidth?
Two of the
most commonly utilised connectivity networks are:
Cellular
Most of us
are very familiar with cellular connectivity as it is used around the world to
connect our mobile phones to the internet. IoT devices also use cell towers to
connect to a cellular network. Cellular connectivity is prolific, has excellent
range and the capacity to send high volumes of data over the network but uses a
lot of power and, therefore, is not ideal for IoT devices which don’t have
access to an immediate power supply and need a long battery life to operate
over long periods of time, for instance in rural or agricultural areas.
LPWAN
‘LPWAN’ stands for Low-Power Wide-Area Network, which is a type of radio
technology and is so far one of the most ideal connectivity networks available
to IoT sensors that are deployed in areas where there is a lack of range. These
devices are usually battery-powered and send very small packets of data over
the network. This connectivity is ideal when it comes to monitoring utilities
such as water, gas and electricity using smart meters and for farming and
agriculture to check on water quality, sensing soil moisture and tracking
livestock.
Computer Vision
Computer
vision is becoming smarter because of more sophisticated algorithms, faster
devices, larger networks and access to a wider range of data sets through IoT.
This allows machines to “see” and analyze in real time.
“Deep
Learning and general AI techniques within computer vision, makes possible what
would be impossible to do by the naked eye.” - Matt Candy, Global leader
for IBM’s iX creative solutions.
Example: Detect
fire and smoke within seconds
Many
threats, such as smoke, are difficult for the human eye to detect in videos,
especially in poor lighting conditions. Seconds later, however, a fire may have
broken out. Security cameras equipped with smoke and fire detection can alert
at an early stage and activate the proper safety measures without any human
assistance.
 |
| Source: Bosch
Security Systems |
Automation
Speed
plays an important role in safety and security. The faster you react to
security incidents, the greater the chance of preventing or at least reducing
damage. In case of theft in a store, every second counts, because criminals may
disappear before security personnel can intervene.
Standard
security surveillance via CCTV wastes valuable time because reaction paths
between machines and human operators are too long. Smart cameras take a shortcut
by saving staff from interpreting videos. They immediately deliver
notifications or initiate appropriate actions themselves.
Example: Detect
and catch thieves in retail
The
"AI Guardman" security camera helps shopkeepers identify potential
thieves in time. Software installed on the camera scans live video streams and
analyzes the poses of any person it can see. This data is automatically matched
against predefined "suspicious" behavior. When it sees something
remarkable, it alerts onsite personnel via app for double checking.
Deep learning
“Cameras
capture the video, but video analytics captures the value.” (IBM)
Using
computers for video analysis is not a new idea. However, there is a problem
that slows the development of video analytics: mobile video made on drones or
vehicles is full of dynamic variables that can confuse even the most
intelligent computers. That's why many companies and startups are working on
smart systems using self-learning algorithms.
Deep
learning is a machine learning method based on artificial neural networks.
Video analytics, which gives security cameras the ability to analyze video data
on board, is one application of deep learning. Another application is
automation, which embeds video analysis into processes.
The good
thing about deep learning is that developers of video analytics apps for
security cameras don't have to reinvent the wheel themselves. There are already
sophisticated frameworks that simplify developing deep learning models, such as
Google's Tensorflow, Microsoft’s Custom Vision and IBM’s PowerAI Vision.
Example: Training
object recognition using IBM’s PowerAI Vision
To determine whether workers are complying with safety regulations such
as wearing helmets, security cameras need to know what helmets look like. In
case a person is not wearing a helmet, a camera could react and alert. This is
what a simplified training process looks like…
Flood Management Assistance
As recent
hurricanes and floods have shown, water damage can be devastating to a community.
That’s why some municipalities are using their city surveillance cameras in
conjunction with water sensor to proactively address the problem.
Water
sensors collect data from multiple sources such as rain gutters, sewer systems
and pump stations, in order to monitor fluctuations in water levels and water
quality. If an alert triggers, having a network camera in proximity to visually
verify the situation helps responders determine the best course of action. For
instance, if multiple water detection sensors trigger alerts simultaneously or
sequentially over a large area it’s probably due to natural runoff from recent
rainfall. But without eyes on the scene, how can you be sure?
Network
camera adds another dimension and timeliness to flood management by helping
responders investigate and identify the cause of a trigger remotely. It might
be a fire hydrant spewing water, a water main break or even a chemical
spill. With video streaming live to the command center, staff can remotely
inspect the area, determine the cause of the trigger and decide whether
remediation is required, thus avoiding the expense of dispatching an
investigative crew to a non-event.
Environmental Control Assistance
Data
centers house the lifeblood of a business so it’s no wonder why companies work
hard to protect them. We’re all familiar with the integration of network
cameras with access control systems to visually verify who is actually using
the credentials.
But
there’s another aspect to protecting data centers and that’s environment
control. Data centers need to maintain optimum humidity and temperature for the
racks of electronics. When environmental sensors in the facility detect
out-of-norm ranges technicians can remotely command a network camera to zoom in
on the gauges and help them determine whether remediation might be necessary.
Coupling
network cameras with other sensors in the data center can provide visual
confirmation of other conditions as well. For instance, every time a data rack
door-open-close sensor detects an event it can trigger the camera to pan to the
location and stream video to security. Some data centers employ weight sensors
at the doorway to weigh personnel and equipment as they enter the room and when
they exit to ensure no additional hardware is being taken out of the facility
or left inside without permission. Any discrepancy would trigger the
camera to zoom in for a close-up of the individual’s face and send a visual
alert and ID information to security.
Roadway Management & Parking Assistance
Network
cameras have long played a part in city-wide traffic management. Adding video
analytics and integration with network sensors, makes those cameras that much
smarter and versatile. They can detect cars driving in bike lanes or
driving in the wrong direction and capture license plates of offenders. Their
ability to detect anomalous traffic flow patterns can be integrated with car
counting sensors, networked electronic road signs and traffic light systems to
automatically redirect vehicles to alternate routes.
They make
great, intelligent parking lot attendants, too. Working in conjunction with
weight sensors network cameras can count vehicles coming into and leaving a lot
or garage and verify when the facility has reached capacity. License plate
recognition and video analytics can be used to ascertain that a vehicle
entering a reserved parking space doesn’t match the credentials and vehicle
attributes in the database.
With the
addition of noise sensors and audio analytics, network cameras can improve roadway
and parking facility safety by detecting and identifying specific sounds –
breaking glass, car alarms, gun shots, and aggressive speech – and triggering a
visual alert to first responders.
Shopper Experience Assistance
In the
early days of online shopping, e-tailers designed their sites to replicate the
in-store customer experience. In an ironic turn of events, today
brick-and-mortar stores are trying to mirror the online shopping experience. To
do so, they’re turning their security systems into adjunct sales assistance.
With network video and audio system automation they can recognize and
acknowledge loyal customers with personal greetings.
With
heatmapping analytics they can measure how much time a customer spends in a
specific department or observe how they walk through the aisles of the store.
They can track shopping behaviors such as items looked at that made it into the
cart or didn’t, or whether a customer actually checked out or left the
merchandise behind. By capturing these shopping patterns and trends retailers
can shape a more positive, more profitable customer shopping experience.
For
instance, integrating video analytics with point of sale systems and RFID
sensors on merchandise tags can result in timely alerts to sales associates to
recommend additional merchandise. This is a case of emulating how e-tailers let
the customer know that other customers who bought X often also purchased items
Y and Z. Or to avoid disappointing customers due to stock outages,
retailers are linking weight sensors and video analytics to make sure their
shelves are well-stocked and if not, quickly alert associates to what items
need to be restocked.
Capturing Business Intelligence
Retailers
are also using video cameras to monitor checkout queues and trigger automated
announcements over the public-address system, closed system such as smartphones
or other wireless communications devices that checkers are needed rather wait
for a person to call for backup.
They’re
applying people counting video analytics to checkout activity to create
rules-based consistency in customer service. While retailers will always use
their surveillance camera for loss prevention, they’re finding that integrating
traditional technology in new ways can yield even bigger returns.
Linking
network video surveillance, video analytics, network communications system and
sensors with point-of-sale systems and customer loyalty databases, retailers
are capturing the business intelligence they need to get back in the game and
make brick-and-mortar a greater overall experience than online shopping.
A Natural Cross-Over Technology
This trend
towards integration has forever changed how organizations view their investment
in security technology. The intelligence and versatility of a tool that can
see, verify and analyze what’s happening in real-time is spurring users to tap
its cross-over potential for a host of other tasks that could benefit from more
astute situational awareness – everything from manufacturing and equipment
maintenance to logistics, inventory control and beyond.
IoT laid
the groundwork for network security solutions to seamlessly integrate with
other IP-based technologies, sensors and programs. How we capitalize on that
connection is only limited by our imagination.