3 Cybersecurity Steps to Reduce Threats to your Electrical System
When anyone mentions cybersecurity, you may automatically think they are referring to IT systems. That is because protecting IT networks – and their associated personal, financial, and other proprietary data – has been the responsibility of IT professionals for an exceptionally long time. But what about your operational technology (OT) infrastructures? Are they also at risk from cyberattacks? How can you protect them? In this post, we’ll discuss these questions, and three specific recommendations for protecting your electrical systems.
The electricity subsector cybersecurity Risk Management Process (RMP) guideline was developed by the Department of Energy (DOE), in collaboration with the National Institute of Standards and Technology (NIST) and the North American Electric Reliability Corporation (NERC).
OT
Cyberattacks: An Increasing Threat
The Ponemon Institute emphatically states that, “Cyberattacks are
relentless and continuous against OT environments.” In a survey of
over 700 organizations from six countries they found that 50 percent had
experienced a cyberattack against their OT infrastructure within the last two
years that resulted in downtime. For large and critical operations, this can be
devastating.
All you need to do is follow the news to see frequent examples of such
attacks. For example, in early 2021, the fast action of a technician narrowly
avoided the risk of thousands of people being poisoned due to a
hacker gaining access to a Florida city’s water treatment plant. Going back a
few years, a breach that came through the HVAC system caused
international retailer Target to have 40 million credit and debit card accounts
compromised, costing them $290 million.
The latter example is just one of many that show why building systems are now widely recognized as OT attack targets. The evolution toward smarter buildings is causing an explosion in the numbers of connected devices – already an estimated 200+ million in commercial buildings alone. With more devices comes more data that needs to be protected, but for facility and business management teams to extract the maximum value, data must be aggregated and shared across OT and IT systems.
This OT/IT
interconnection means that a cyberattack on an OT system can:
·
Compromise
operational safety or the health of building occupants
·
Impact
productivity by taking down production lines or other equipment and processes;
more about the relationship between Cybersecurity and Productivity.
· Ultimately cause an IT threat by passing malware or a virus from the OT to IT infrastructure
The Attack
Surface is Now Larger
Essentially, connected OT infrastructures have increased the ‘attack
surface’ for hackers and, in many cases, have acted as an organization’s
Achilles heel. Clearly, it is not enough anymore to focus attention only on
protecting IT and data systems integrity. All organizations must ensure strong
OT cybersecurity is in place.
But what OT systems are we talking about? Depending on your type of
operation, these can include industrial automation systems (e.g. SCADA)
and smart building systems like a building management system (BMS), building
security, lighting systems, and the energy and power management
system (EPMS) overseeing your facility’s electrical distribution. Navigant
Research notes, “Cybersecurity issues are expected to grow in tandem with the
digital transformation of real estate through intelligent building
technologies.”
In this post, we will consider cybersecurity specifically for your EPMS and electrical distribution system. However, these recommendations and practices equally apply to other OT systems.
Connected
Power Means Greater Vulnerability
Energy and
power management systems are helping organizations boost efficiency and
sustainability, optimize operating costs, maximize uptime, and get better
performance and longevity from electrical assets. When combined with BMS, an
EPMS can also help make the work environment healthier and more productive for
occupants.
Enabling
these EPMS benefits is a connected network of smart metering, analysis,
control, and protection devices that share data continuously with
onsite and/or cloud-based EPMS applications. The application provides extensive
monitoring and analytics while providing mobile access to data and alerts to
all facility stakeholders. Connection to the cloud also opens the door to
expert power and asset advisory support that can augment a
facility’s onsite team with 24/7 monitoring, predictive maintenance,
energy management, and other services.
All these
onsite, cloud, and mobile connections offer a potential target and entry for
hackers so you can read our facility managers guide to building systems
and cybersecurity.
Securing
Your Electrical System: A Holistic Approach
A hacker only needs to find one ‘hole’ in one system, at one point of time, to be successful. What you need is a holistic approach to ensure that all potential vulnerabilities are secured. For new buildings, cybersecurity best practices should be a part of the design of all OT systems. For existing buildings, cybersecurity should be addressed when OT systems are starting to be digitized. For both scenarios, the following are three key considerations:
1.
Seek Specialized, Expert Assistance
The
priorities for IT systems are confidentiality, integrity, and availability. For
OT, the top priorities are safety, resilience, and confidentiality. This means
that OT security upgrades or problems need to be addressed in a different way
from IT, with careful planning and procedures. For these reasons, you need to
choose a cybersecurity partner who has proper OT experience, to help you comply
with all relevant cybersecurity standards and best practices.
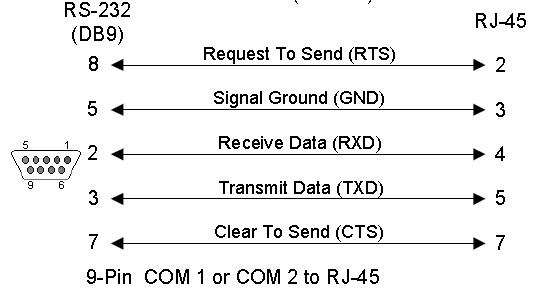
OT systems
also use different communication protocols compared to IT systems, such as
BACNet, Modbus, etc. If you had your IT team attempt to perform OT security
system scans, those scanning tools might cause serious conflicts, risking an OT
system shutdown.
Cyberthreats are also constantly evolving, so you should seek a partner who offers ongoing OT monitoring services, updates, system maintenance, and incident response. All of these should be available remotely.
2.
Put the Right Controls in Place
An OT cybersecurity specialist will help audit your EPMS and electrical
systems to assess the current vulnerabilities and risks, including the gaps in
any procedures and protocols.
You and the specialist must determine how secure your electrical system
needs to be. The IEC 62443 standard helps protect IoT-enabled OT
systems by defining seven foundational requirements (e.g. access
control, use control, availability, response, etc.), each of which are
designated a security level. Increased security levels offer greater protection
against more sophisticated attacks. Your cybersecurity partner will help you
determine the level of security you need for each requirement.
An example of one technique for securing networked systems is to break
up systems into ‘zones,’ with each secured individually. OT will be separated
from IT, and within OT there may be further segregation. A special
‘demilitarized’ zone is typically included, which is a perimeter subnetwork
that sits between the public and private networks for an added layer of
security. This makes it harder for hackers to find a way in from one system or
zone to another. Where required, connections between networks are provided by
specially secured data ‘conduits.’
Your electrical system should also be physically secured, with no access by unauthorized personnel. This same strategy applies to EPMS communications network security by means of controlled, multi-tiered permission-based access.
3. Train your Staff
Many cyberattacks are successful because employees have caused
unintended errors. It is important that your people become aware of, and
vigilant against, cyberthreats. This includes giving your operations team
specialized OT cybersecurity training.
This training will typically include multiple steps, including training all individuals to spot social engineering cues, such as phishing attempts or attempts to access protected areas using pretexting (i.e. someone pretending to be a vendor to gain access). This will also include establishing protocols around the use of passwords, multi-factor authorization, policies around WiFi access (e.g., guest network that remains isolated from OT networks), regular auditing of user accounts and permissions, etc.
While the horizontal cybersecurity framework provides a solid basis, specific characteristics of the energy sector such as the need for fast reaction, risks of cascading effects and the need to combine new digital technology with older technologies necessitate specific legislation.
Thanks to Felix Ramos & Khaled Fakhuri to write this
article.